Difference between revisions of "Journal:Cyberbiosecurity: A new perspective on protecting U.S. food and agricultural system"
Shawndouglas (talk | contribs) (Saving and adding more.) |
Shawndouglas (talk | contribs) (Saving and adding more.) |
||
| Line 64: | Line 64: | ||
The food and agricultural industries are at a critical point as the development and use of biological, genetic, precision, and information technologies expand and intersect. Collectively, there is a need to evaluate potential liabilities and understand the vulnerabilities of biological and genetic data systems. | The food and agricultural industries are at a critical point as the development and use of biological, genetic, precision, and information technologies expand and intersect. Collectively, there is a need to evaluate potential liabilities and understand the vulnerabilities of biological and genetic data systems. | ||
==Risk assessment, critical control points, and regulatory options== | |||
Cybersecurity risk assessment for industrial control systems (ICS) is advancing rapidly. Cherdantseva ''et al.''<ref name="CherdantsevaARev16">{{cite journal |title=A review of cyber security risk assessment methods for SCADA systems |journal=Computers & Security |author=Cherdantseva, Y.; Burnap, P.; Blyth, A. et al. |volume=56 |pages=1–27 |year=2016 |doi=10.1016/j.cose.2015.09.009}}</ref> reviewed 24 different cybersecurity risk assessment methods relevant to ICS. Applications of such risk assessment approaches in the food and agriculture sectors have not been evaluated, and the complexity and diversity of those sectors may not conform to the current cybersecurity risk assessment methods. Cyberbiosecurity risk assessment strategies that address the unique security challenges at the intersection of the biological, physical, and cyberspace are important for protecting the food and agriculture system. | |||
Food manufacturers use the principles of Hazard Analysis and Critical Control Points (HACCP) to assure the production of safe products. HACCP is a familiar risk assessment process within the food and agriculture system. This management system looks at the likely occurrence of a chemical, biological, or physical food safety hazard in the manufacturing process and the controls that can be put in place to reduce, eliminate, or control the potential hazard. HACCP principles use critical control points (CCPs) as steps in a process where specific controls can be implemented to control, reduce, or eliminate a hazard. HACCP principles are used around the world for the production of safe food products and are required by the [[United States Department of Agriculture|U.S. Department of Agriculture]]'s Food Safety Inspection Service and the U.S. [[Food and Drug Administration]]. A risk matrix (see Table 1 in the Supplemental Material) may be used to identify potential vulnerabilities and estimate likelihood of occurrence with the potential public health and financial consequences. An example using HACCP principles for an assessment of an industrial laboratory processing biological and genetic materials is presented in the Supplemental Material. In this specific example, two CCPs (alternative supplier verification of biological and genetic materials program, and cyber biosecurity data verification program) were identified to mitigate potential risks. Four control point programs (supplier approval, employee training, security programs, and good laboratory standard operating procedures) were identified to support the overarching process for cyber biosecurity. | |||
Several economic problems confront policymakers when addressing cyber biosecurity in the food and agriculture sector. The most pressing concerns are externalities caused by the networked nature of the system and the misaligned incentives of individual agents. The risks associated with cyber biosecurity threats and harm to society are likely to be larger than the losses suffered by an individual entity; individual firms may not have incentives to provide socially optimal levels of security for the network. Furthermore, if agents know that their own protection depends on security investments made by others, they may become free-riders. Again, this results in inadequate private provision of the public good or security of the network.<ref name="VarianSystem04">{{cite book |chapter=System Reliability and Free Riding |title=Economics of Information Security |author=Varian, H. |editor=Camp, L.J.; Lewis, S. |series=Advances in Information Security |volume=12 |publisher=Springer |year=2004 |pages=1–15 |isbn=9781402080906 |doi=10.1007/1-4020-8090-5_1}}</ref> | |||
Multiple regulatory and policy options exist to counter threats to the food and agriculture system. In some cases, it may be easier to implement protections within these sectors because agribusinesses are already subject to relatively strict disclosure regulations. Information disclosure provides regulators with the data necessary to align individual incentives with the security of the system as a whole. This could be done with top-down regulation, changes to the assignment of liability, or the development of market-based systems for the control of cyber biosecurity risks. For instance, the development of cyber biosecurity insurance markets could be encouraged. Regardless of eventual policy measures, it will be important to ensure that the costs of protecting the system are properly aligned with the probabilities of loss and magnitudes of loss associated with cyber biosecurity threats. The most efficient methods of securing the food and agriculture system are likely to rely on a variety of regulatory approaches. | |||
==Considering the diversity within and across plant, animal, and environmental sectors of the food and agricultural system== | |||
The HACCP concept assesses risk and establishes CCPs for a specific facility and cannot be generalized effectively to all food manufacturing plants. Applying this concept to cyber biosecurity risk, control points, and CCPs, therefore, is challenged by the diversity of enterprises within a sector and across the food and agriculture system. Within each sector are unique suppliers providing biological material, chemicals and ingredients, robotics and machinery, software, data, and data storage systems. Some of the security measures are encompassed by cyber security, cyberphysical security, and biosecurity/biosafety practices, at least for large corporate entities with sufficient resources. However, an unsecured system from a small agribusiness supplier, producer, processor, or commodity cooperative could introduce risk. | |||
We use the illustration of a train with multiple boxcars as an example of various sectors within one commodity sector of the food and agriculture system (Figure 2, top). The various cars represent the transition from genetics and breeding through production, processing, distribution, and consumer purchase/use. The exchange of information between the different sectors is often limited, as illustrated by the couplings. The role of the federal government policies and programs provide support and guidance (tracks). Suppliers and other support systems access one or more sectors within a commodity system. The system is driven (engine) by general public (consumers) acceptance of practices and goods, or their fear and mistrust if a risk or threat is perceived. If any stage “derails” or if any supporting agency or organization “buckles” due to a cyber biosecurity threat or attack, the entire system is at risk, with subsequent risk to the U.S. food supply and the bio economy (Figure 2, bottom). Currently, the cyber security industry is not visibly involved in protecting biological data interfacing with the cyber-physical infrastructure supporting the food and agriculture system. | |||
[[File:Fig2 Duncan FrontBioengBiotech2019 7.jpg|900px]] | |||
{{clear}} | |||
{| | |||
| STYLE="vertical-align:top;"| | |||
{| border="0" cellpadding="5" cellspacing="0" width="900px" | |||
|- | |||
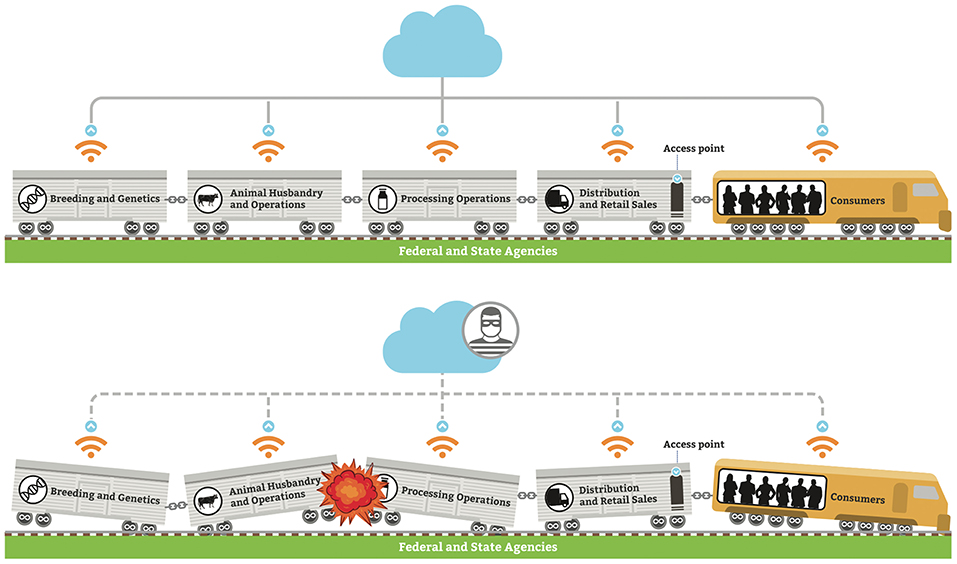
| style="background-color:white; padding-left:10px; padding-right:10px;"| <blockquote>'''Fig. 2''' '''(Top)''' Food and agriculture system for each commodity sector is a sequence of stages, with limited communications and sharing of data between each; '''(Bottom)''' if a cyber-biosecurity event occurs, it can have catastrophic effect on the entire food and agriculture system.</blockquote> | |||
|- | |||
|} | |||
|} | |||
Some potential mitigations to the issues are possible. Cyber biosecurity planning and implementation are needed to protect the intellectual and physical (data) property associated with such food and agriculture priorities. Examples include: | |||
* Plant and animal germplasm, such as old world corn germplasm, microbiology collection (pathogens, fermentation, microbiome) repositories, including economic assessment and protection of data sharing; | |||
* Biocontrolled systems or processes, such as “smart” technology greenhouse data; | |||
* Animal and plant disease diagnostic networks and information sharing; | |||
* Fermentation processing and thermal processing control parameters; and | |||
* Freshwater and drinking water supplies and treatment systems. | |||
We further illustrate by outlining some unique considerations for various food and agriculture commodities. | |||
===Dairy=== | |||
Selection of genetics for breeding is key to the high milk production in the U.S. dairy industry. Genetic data is highly evaluated as part of the process for breeding. Milk production records are important for establishing high-performance animals. While there are some very large dairy herds (>2,000 animals), the U.S. dairy industry is dominated by small to medium farms, many of whom sell their milk through a cooperative structure. Herd health records and drug use are regulated. Data security is variable, and often limited. Fluid milk and dairy food processors do not have detailed records of individual cow production or farm production practices, creating a gap in tracing of information and potential for data breach. Processors utilize computer systems for maintaining processing temperatures, ingredient additions, sanitizing, and cleaning steps. | |||
==References== | ==References== | ||
Revision as of 23:15, 8 April 2019
| Full article title | Cyberbiosecurity: A new perspective on protecting U.S. food and agricultural system |
|---|---|
| Journal | Frontiers in Bioengineering and Biotechnology |
| Author(s) |
Duncan, Susan E.; Reinhard, Robert; Williams, Robert C.; Ramsey, Ford; Thomason, Wade; Lee, Kiho; Dudek, Nancy; Mostaghimi, Saied; Colbert, Edward; Murch, Randall |
| Author affiliation(s) | Virginia Tech, Tyson Foods |
| Primary contact | Email: duncans at vt dot edu |
| Editors | Morse, Stephen Allen |
| Year published | 2019 |
| Volume and issue | 7 |
| Page(s) | 63 |
| DOI | 10.3389/fbioe.2019.00063 |
| ISSN | 2296-4185 |
| Distribution license | Creative Commons Attribution 4.0 International |
| Website | https://www.frontiersin.org/articles/10.3389/fbioe.2019.00063/full |
| Download | https://www.frontiersin.org/articles/10.3389/fbioe.2019.00063/pdf (PDF) |
Abstract
Our national data and infrastructure security issues affecting the “bioeconomy” are evolving rapidly. Simultaneously, the conversation about cybersecurity of the U.S. food and agricultural system (cyber biosecurity) is incomplete and disjointed. The food and agricultural production sectors influence over 20% of the nation's economy ($6.7T) and 15% of U.S. employment (43.3M jobs). The food and agricultural sectors are immensely diverse, and they require advanced technologies and efficiencies that rely on computer technologies, big data, cloud-based data storage, and internet accessibility. There is a critical need to safeguard the cyber biosecurity of our bioeconomy, but currently protections are minimal and do not broadly exist across the food and agricultural system. Using the food safety management Hazard Analysis Critical Control Point (HACCP) system concept as an introductory point of reference, we identify important features in broad food and agricultural production and food systems: dairy, food animals, row crops, fruits and vegetables, and environmental resources (water). This analysis explores the relevant concepts of cyber biosecurity from food production to the end product user (such as the consumer) and considers the integration of diverse transportation, supplier, and retailer networks. We describe common challenges and unique barriers across these systems and recommend solutions to advance the role of cyber biosecurity in the food and agricultural sectors.
Keywords: plant, animal, food, cyber biosecurity, biosecurity, cyber security, agriculture, bioeconomy
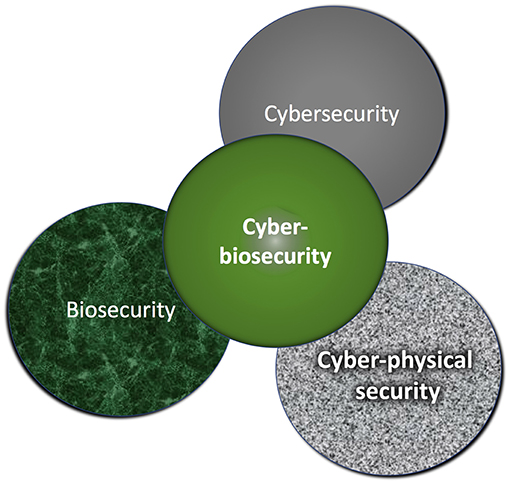
Introduction: Food and agriculture cyberbiosecurity at the interface of biosecurity and cybersecurity
Public trust and confidence in the food supply are critical and influential on acceptance of data-driven innovations and technologies within the food and agriculture systems. Cyberbiosecurity is a nascent paradigm and discipline at the interface of biosafety/biosecurity, cybersecurity, and cyber-physical security (Figure 1).[1] This new discipline has emerged alongside “big data” with the extensive and ever-increasing reliance of the life sciences on information systems technologies, rapid and profitable expansion of life science discoveries, and the growth of the U.S. bioeconomy. Protecting biological data and information within the life sciences has unique differences from the more familiar biosafety and biosecurity approaches.[2] While the latter two categories address biological risks and threats, they do not protect against harm created when computational and information technology-dependent systems are threatened or corrupted. Just as food safety regulations target the protection of human health, incorporating cyber biosecurity strategies for the food and agriculture industries is a protective step in securing the food supply. Such efforts have the power to positively influence lives and protect the bioeconomy. Cyberbiosecurity can improve the security and stability of domestic and global food and agriculture systems. United States innovation in this realm is routinely studied and adopted around the globe, and as such, the U.S. can provide insight and leadership in cyber biosecurity of global food and agriculture systems.
|
Integrated scientific, mathematical, computational, and engineering advancements in regenerative biology, genetics and breeding technologies, plant-derived vaccine and animal therapies, biological design and testing automation, and other activities are rapidly leading to development of biotechnological and agricultural applications of direct relevance to the food and agriculture system.[3][4] The translation and application of data-driven technologies for precision agriculture, autonomous systems, bio-automated processing and data recording, and other technologies yields large data sets of economic and bio-based information for agribusinesses.[5] Such advances require high throughput processing, data management and integration, bio-automation, and other computer-based management of biological data. These advances increase efficiencies, decision processes, and output within the food and agricultural system. However, such information is susceptible to ownership policy challenges, theft, and cyberattack as users may not be alert to potential vulnerabilities nor be trained in effective protections and security strategies.[5][6] Unprotected or weakly protected systems are susceptible to unwanted surveillance, intrusions into data systems, and cyber-activities targeted toward malicious attack. Cyberbiosecurity threats include inappropriate access to systems, data, or analytical technologies and the use or corruption of the information accessed to cause harm within life science-focused research, production, processing, and use. Examples of data-driven, high-value food and agricultural products susceptible to cyber threat include high-yielding and specialty agricultural crops, high performance livestock, biopharma fermented molecules developed through advanced breeding and genomics, biotechnology advancements, and “big data” analyses.[7] As technology advances, all parts of society, from governmental agencies to public health and manufacturing, rely more on advanced biological systems with big data and technologies that utilize such information. The identification and mitigation of cyber biosecurity threats will become increasingly important.
Vulnerability of the food and agricultural system and the bioeconomy
The U.S. food and agriculture system, influencing 20% ($6.7T) of the domestic bio economy[8], represents a significant risk to global food security. The data science market value for agriculture is estimated in excess of $20B.[5] The food and agriculture system is composed of many sectors that are not well-integrated, is widely dispersed geographically, and has huge diversity in size (number of employees) and capacity. Most of the economic value is generated by large, multinational corporate enterprises. Conversely, small family-owned farming operations account for 90% of U.S. farms, which yield 24% of the value of agricultural production.[9]
The family small-business agricultural enterprise (family farm) has economic and social distinctions from corporate farms. Small farm producers view their data with a sense of personal privacy and protection.[5] Small businesses often use their internet-linked home computer for both personal and business activities, increasing the risk of cyber-attack[10][11]; over 20% of small businesses get hacked.[11] Generally, small farms and agribusinesses are not comfortable adopting computer security technology (selecting, configuring, managing) although they recognize its relevance and value. Moderate-sized agribusinesses, including many food processing companies and supporting industries, are vulnerable since cyberattacks are often targeted against organizations with more than 100 employees.[11] Additionally, the food and agriculture system includes military food production—such as the manufacturing of packaged meals for soldiers—which has a high potential for sabotage.[12] It is important to note that attackers need not know details of the food manufacturing process. Attackers need only know technical methods for exploiting the machinery or the process, such as lowering the temperature on meat cookers before packaging.[13][14]
The incorporation of cyber-based technologies and data driven solutions in farm production, food processing, supplier industries, transport of goods, regulatory oversight, and marketing sales and communication with consumers creates a paradigm shift.[6] Cloud-based storage of large data sets, use of open-sourced or internet/cloud-based software, and corporate management of proprietary software each increase opportunities for data access by unauthorized users. Within the food and agriculture system, the use of biological and genetic analytical technologies within research laboratories is widespread for the evaluation of food quality, identification of zoonotic disease, and animal and plant health. Additionally, the use of bioinformatics and genetic technologies is enhancing the rate of development of new products and crops. Public trust and acceptance are key to incorporating advanced technologies into the food and agriculture system.[4][15] Interdependency of information technology with biological output creates opportunities for new bio-threats, which can harm public trust; transparency is valued.[7] When public opinion is turned against a technical advancement, policy and protection strategies may cause more harm than the actual threat itself.[4]
Holistically, the ramifications of a failure to provide cyber biosecurity of the food and agriculture system fall into several general categories[6]:
- Threats to confidentiality—data privacy
- Data exposure (e.g., naïve exposure of data by individuals, cyber security gaps in small businesses, or laboratories to potential threats)
- Capturing private data with intent to aggregate data for profit or predictive advantage
- Threats to integrity—theft or destruction of intellectual property/productivity disruptions, and safety risks
- Intellectual property theft (e.g., advances in plant and animal varieties and genetics)
- Manipulation of critical automated (computer-based) processes (e.g., thermal processing time and temperature for food safety)
- Seizing control of robotics or autonomous vehicles (e.g., failure to perform, overriding of precise function)
- Threats to availability—disruption of agricultural/food production and supply
- Misinformation influencing trust and cooperation within the food and agriculture system and/or consumers
- Lack of equipment, supplies, or end-products to meet expectations
- Lack of ability to perform vulnerability assessments and develop emergency response plans (e.g., protection of rivers, surface waters, and drinking water supplies)
The food and agricultural industries are at a critical point as the development and use of biological, genetic, precision, and information technologies expand and intersect. Collectively, there is a need to evaluate potential liabilities and understand the vulnerabilities of biological and genetic data systems.
Risk assessment, critical control points, and regulatory options
Cybersecurity risk assessment for industrial control systems (ICS) is advancing rapidly. Cherdantseva et al.[16] reviewed 24 different cybersecurity risk assessment methods relevant to ICS. Applications of such risk assessment approaches in the food and agriculture sectors have not been evaluated, and the complexity and diversity of those sectors may not conform to the current cybersecurity risk assessment methods. Cyberbiosecurity risk assessment strategies that address the unique security challenges at the intersection of the biological, physical, and cyberspace are important for protecting the food and agriculture system.
Food manufacturers use the principles of Hazard Analysis and Critical Control Points (HACCP) to assure the production of safe products. HACCP is a familiar risk assessment process within the food and agriculture system. This management system looks at the likely occurrence of a chemical, biological, or physical food safety hazard in the manufacturing process and the controls that can be put in place to reduce, eliminate, or control the potential hazard. HACCP principles use critical control points (CCPs) as steps in a process where specific controls can be implemented to control, reduce, or eliminate a hazard. HACCP principles are used around the world for the production of safe food products and are required by the U.S. Department of Agriculture's Food Safety Inspection Service and the U.S. Food and Drug Administration. A risk matrix (see Table 1 in the Supplemental Material) may be used to identify potential vulnerabilities and estimate likelihood of occurrence with the potential public health and financial consequences. An example using HACCP principles for an assessment of an industrial laboratory processing biological and genetic materials is presented in the Supplemental Material. In this specific example, two CCPs (alternative supplier verification of biological and genetic materials program, and cyber biosecurity data verification program) were identified to mitigate potential risks. Four control point programs (supplier approval, employee training, security programs, and good laboratory standard operating procedures) were identified to support the overarching process for cyber biosecurity.
Several economic problems confront policymakers when addressing cyber biosecurity in the food and agriculture sector. The most pressing concerns are externalities caused by the networked nature of the system and the misaligned incentives of individual agents. The risks associated with cyber biosecurity threats and harm to society are likely to be larger than the losses suffered by an individual entity; individual firms may not have incentives to provide socially optimal levels of security for the network. Furthermore, if agents know that their own protection depends on security investments made by others, they may become free-riders. Again, this results in inadequate private provision of the public good or security of the network.[17]
Multiple regulatory and policy options exist to counter threats to the food and agriculture system. In some cases, it may be easier to implement protections within these sectors because agribusinesses are already subject to relatively strict disclosure regulations. Information disclosure provides regulators with the data necessary to align individual incentives with the security of the system as a whole. This could be done with top-down regulation, changes to the assignment of liability, or the development of market-based systems for the control of cyber biosecurity risks. For instance, the development of cyber biosecurity insurance markets could be encouraged. Regardless of eventual policy measures, it will be important to ensure that the costs of protecting the system are properly aligned with the probabilities of loss and magnitudes of loss associated with cyber biosecurity threats. The most efficient methods of securing the food and agriculture system are likely to rely on a variety of regulatory approaches.
Considering the diversity within and across plant, animal, and environmental sectors of the food and agricultural system
The HACCP concept assesses risk and establishes CCPs for a specific facility and cannot be generalized effectively to all food manufacturing plants. Applying this concept to cyber biosecurity risk, control points, and CCPs, therefore, is challenged by the diversity of enterprises within a sector and across the food and agriculture system. Within each sector are unique suppliers providing biological material, chemicals and ingredients, robotics and machinery, software, data, and data storage systems. Some of the security measures are encompassed by cyber security, cyberphysical security, and biosecurity/biosafety practices, at least for large corporate entities with sufficient resources. However, an unsecured system from a small agribusiness supplier, producer, processor, or commodity cooperative could introduce risk.
We use the illustration of a train with multiple boxcars as an example of various sectors within one commodity sector of the food and agriculture system (Figure 2, top). The various cars represent the transition from genetics and breeding through production, processing, distribution, and consumer purchase/use. The exchange of information between the different sectors is often limited, as illustrated by the couplings. The role of the federal government policies and programs provide support and guidance (tracks). Suppliers and other support systems access one or more sectors within a commodity system. The system is driven (engine) by general public (consumers) acceptance of practices and goods, or their fear and mistrust if a risk or threat is perceived. If any stage “derails” or if any supporting agency or organization “buckles” due to a cyber biosecurity threat or attack, the entire system is at risk, with subsequent risk to the U.S. food supply and the bio economy (Figure 2, bottom). Currently, the cyber security industry is not visibly involved in protecting biological data interfacing with the cyber-physical infrastructure supporting the food and agriculture system.
|
Some potential mitigations to the issues are possible. Cyber biosecurity planning and implementation are needed to protect the intellectual and physical (data) property associated with such food and agriculture priorities. Examples include:
- Plant and animal germplasm, such as old world corn germplasm, microbiology collection (pathogens, fermentation, microbiome) repositories, including economic assessment and protection of data sharing;
- Biocontrolled systems or processes, such as “smart” technology greenhouse data;
- Animal and plant disease diagnostic networks and information sharing;
- Fermentation processing and thermal processing control parameters; and
- Freshwater and drinking water supplies and treatment systems.
We further illustrate by outlining some unique considerations for various food and agriculture commodities.
Dairy
Selection of genetics for breeding is key to the high milk production in the U.S. dairy industry. Genetic data is highly evaluated as part of the process for breeding. Milk production records are important for establishing high-performance animals. While there are some very large dairy herds (>2,000 animals), the U.S. dairy industry is dominated by small to medium farms, many of whom sell their milk through a cooperative structure. Herd health records and drug use are regulated. Data security is variable, and often limited. Fluid milk and dairy food processors do not have detailed records of individual cow production or farm production practices, creating a gap in tracing of information and potential for data breach. Processors utilize computer systems for maintaining processing temperatures, ingredient additions, sanitizing, and cleaning steps.
References
- ↑ Murch, R.S.; So, W.K.; Buchholz, W.G. et al. (2018). "Cyberbiosecurity: An Emerging New Discipline to Help Safeguard the Bioeconomy". Frontiers in Bioengineering and Biotechnology 6: 39. doi:10.3389/fbioe.2018.00039.
- ↑ Peccoud, J.; Gallegos, J.E.; Murch, R. et al. (2018). "Cyberbiosecurity: From Naive Trust to Risk Awareness". Trends in Biotechnology 36 (1): 4–7. doi:10.1016/j.tibtech.2017.10.012. PMID 29224719.
- ↑ Board on Chemical Sciences and Technology; Board on Life Sciences (2014). Meeting Recap: Workshop - Convergence: Safeguarding Technology in the Bioeconomy. The National Academies of Sciences, Engineering, and Medicine.
- ↑ 4.0 4.1 4.2 Wintle, B.C.; Boehm, C.R.; Rhodes, C. et al. (2017). "A transatlantic perspective on 20 emerging issues in biological engineering". eLife 3: e30247. doi:10.7554/eLife.30247. PMC PMC5685469. PMID 29132504. https://www.ncbi.nlm.nih.gov/pmc/articles/PMC5685469.
- ↑ 5.0 5.1 5.2 5.3 Sykuta, M.E. (2016). "Big data in agriculture: Property rights, privacy and competition in ag data services". International Food and Agribusiness Management Review 19 (A): 57–74. https://www.ifama.org/Volume-19-Issue-A.
- ↑ 6.0 6.1 6.2 Boghossian, A.; Linsky, S.; Brown, A. et al. (2018). "Threats to Precision Agriculture" (PDF). U.S. Department of Homeland Security. https://www.dhs.gov/sites/default/files/publications/2018%20AEP_Threats_to_Precision_Agriculture.pdf. Retrieved 08 January 2019.
- ↑ 7.0 7.1 Board on Chemical Sciences and Technology (2015) (PDF). Meeting Recap: Safeguarding the Bioeconomy: Applications and Implications of Emerging Science. The National Academies of Sciences, Engineering, and Medicine. https://www.ehidc.org/sites/default/files/resources/files/Safeguarding%20the%20Bioeconomy_II_Recap%20Final%20090815.pdf.
- ↑ "What is the Food and Ag Industries’ Impact in Your Community?". Feeding the Economy. 2018. https://feedingtheeconomy.com/. Retrieved 28 October 2018.
- ↑ MacDonald, J.M.; Hoppe, R.A. (6 March 2017). "Large Family Farms Continue To Dominate U.S. Agricultural Production". Amber Waves. U.S. Department of Agriculture. https://www.ers.usda.gov/amber-waves/2017/march/large-family-farms-continue-to-dominate-us-agricultural-production/. Retrieved 28 October 2018.
- ↑ National Agricultural Statistics Service (20 August 2013). "Farm Computer Usage and Ownership". U.S. Department of Agriculture. https://usda.library.cornell.edu/concern/publications/h128nd689?locale=en. Retrieved 27 October 2018.
- ↑ 11.0 11.1 11.2 Geil, A.; Sagers, G.; Spaulding, A.D. et al.. "Cyber security on the farm: An assessment of cyber security practices in the United States agriculture industry". International Food and Agribusiness Management Review 21: 317–34. doi:10.22434/IFAMR2017.0045.
- ↑ Colbert, E.J.M.; Kott, A.; Knachel, L.P.. "The game-theoretic model and experimental investigation of cyber wargaming". The Journal of Defense Modeling and Simulation: Applications, Methodology, Technology: 1–18. doi:10.1177/1548512918795061.
- ↑ Colbert, E.; Sullivan, D.; Wong, K. et al. (2015). Table-Top Exercise Final Report: Intrusion Detection Capabilities for US Army SCADA Systems: Information Packet. US Army Research Lab Technical Report ARL-TR-7498.
- ↑ Colbert, E.; Sullivan, D.; Wong, K. et al. (2015). RED and BLUE Teaming of a US Army SCADA System: Table-Top Exercise Final Report. US Army Research Lab Technical Report ARL-TR-7497.
- ↑ National Institute of Food and Agriculture (1 November 2016). "Data Summit: Changing the Face, Place, and Space of Agriculture" (PDF). U.S. Department of Agriculture. https://nifa.usda.gov/sites/default/files/resource/Stakeholder%20Ideas%20Engine%20Input%20-%20Summary%5B1%5D.pdf. Retrieved 28 October 2018.
- ↑ Cherdantseva, Y.; Burnap, P.; Blyth, A. et al. (2016). "A review of cyber security risk assessment methods for SCADA systems". Computers & Security 56: 1–27. doi:10.1016/j.cose.2015.09.009.
- ↑ Varian, H. (2004). "System Reliability and Free Riding". In Camp, L.J.; Lewis, S.. Economics of Information Security. Advances in Information Security. 12. Springer. pp. 1–15. doi:10.1007/1-4020-8090-5_1. ISBN 9781402080906.
Notes
This presentation is faithful to the original, with only a few minor changes to presentation, grammar, and punctuation. In some cases important information was missing from the references, and that information was added.