Journal:Assessing cyberbiosecurity vulnerabilities and infrastructure resilience
| Full article title | Assessing cyberbiosecurity vulnerabilities and infrastructure resilience |
|---|---|
| Journal | Frontiers in Bioengineering and Biotechnology |
| Author(s) | Schabacker, Daniel S.; Levy, Leslie-Anne; Evans, Nate J.; Fowler, Jennifer M.; Dickey, Ellen A. |
| Author affiliation(s) | Argonne National Laboratory |
| Primary contact | Email: dschabacker at anl dot gov |
| Editors | DiEuliis, Diane |
| Year published | 2019 |
| Volume and issue | 7 |
| Page(s) | 61 |
| DOI | 10.3389/fbioe.2019.00061 |
| ISSN | 2296-4185 |
| Distribution license | Creative Commons Attribution 4.0 International |
| Website | https://www.frontiersin.org/articles/10.3389/fbioe.2019.00061/full |
| Download | https://www.frontiersin.org/articles/10.3389/fbioe.2019.00061/pdf (PDF) |
|
|
This article should not be considered complete until this message box has been removed. This is a work in progress. |
Abstract
The convergence of advances in biotechnology with laboratory automation, access to data, and computational biology has democratized biotechnology and accelerated the development of new therapeutics. However, increased access to biotechnology in the digital age has also introduced additional security concerns and ultimately spawned the new discipline of cyberbiosecurity, which encompasses cybersecurity, cyber-physical security, and biosecurity considerations. With the emergence of this new discipline comes the need for a logical, repeatable, and shared approach for evaluating facility and system vulnerabilities to cyberbiosecurity threats. In this paper, we outline the foundation of an assessment framework for cyberbiosecurity, accounting for both security and resilience factors in the physical and cyber domains. This is a unique problem set, yet despite the complexity of the cyberbiosecurity field in terms of operations and governance, previous experience developing and implementing physical and cyber assessments applicable to a wide spectrum of critical infrastructure sectors provides a validated point of departure for a cyberbiosecurity assessment framework. This approach proposes to integrate existing capabilities and proven methodologies from the infrastructure assessment realm (e.g., decision science, physical security, infrastructure resilience, cybersecurity) with new expertise and requirements in the cyberbiosecurity space (e.g., biotechnology, biomanufacturing, genomics) in order to forge a flexible and defensible approach to identifying and mitigating vulnerabilities. Determining where vulnerabilities reside within cyberbiosecurity business processes can help public and private sector partners create an assessment framework to identify mitigation options for consideration that are both economically and practically viable and, ultimately, allow them to manage risk more effectively.
Keywords: cyberbiosecurity, vulnerability, resilience, risk, convergence, emerging, converging, technology
Introduction
An important initial step in effectively managing risk is developing a comprehensive understanding of vulnerabilities. Stakeholders can then identify economical and practical options to mitigate vulnerabilities. Risk in the biological sciences has been managed through the implementation of standard biosecurity practices, through which vulnerabilities are (a) identified and (b) mitigated through regularly updated training, policies, and enhanced physical security. To prevent unauthorized access to high-consequence biological agents, the U.S. Government (USG) stood up the Federal Select Agent Program (FSAP), which added extensive requirements (e.g., background checks, registration by institutions, increased oversight) for those seeking access to "biological select agents and toxins" (BSATs). The BSAT list is based on taxonomic classifications and includes 67 high-consequence biological agents and toxins. Advances in genetic engineering tools (e.g., CRISPR Cas 9 systems) along with the convergence of lab automation, computational biology, and access to publicly available genomic databases will dramatically impact the effectiveness of the FSAP as well as other biosecurity policies and practices. It will no longer be necessary to obtain physical samples to exploit a biological agent; access to publicly available genomic databases, biofoundries, lab automation, and computational biology enables the design and production of high-consequence biological agents and toxins. These biological agents may be entirely new to nature and unconstrained by taxonomic classification such as the BSAT list.[1] This new digital environment in which biological research increasingly takes place must be systematically assessed for vulnerabilities in order to effectively manage evolving risks. The new discipline of cyberbiosecurity—which includes biosecurity, cyber-physical security, and cybersecurity—directly addresses the unique risks associated with biotechnology in an increasingly digital environment.[2][3]
In this paper, we outline the foundation of an assessment framework for cyberbiosecurity, accounting for both security and resilience factors in the physical and cyber domains. When implemented, the assessment framework will help partners identify and prioritize vulnerabilities. Importantly, the prioritization of vulnerabilities will result from a defensible, transparent, and reproducible assessment. In conjunction with an understanding of the consequences of disruption, risk mitigation strategies can be developed and considered in return-on-investment (ROI) analyses. ROIs will allow stakeholders to make informed decisions on how best to allocate limited resources for maximum impact.
While biosecurity is one of the three disciplines comprising cyberbiosecurity (e.g., biosecurity, cyber-physical security, and cybersecurity), it is well-established and will not be discussed due to space limitations.
Risk mitigation in the era of converging technologies
Emerging and converging technologies present new risks to security that require new methodologies for risk prioritization and mitigation.
The accelerated pace of technological advancements across nearly all scientific disciplines has been driven largely by the convergence of advancements in scientific disciplines associated with computation, networking, automation, and access to data. Convergence occurs where scientific disciplines or key enabling technologies combine with other disciplines or enabling technologies and promise new or improved capabilities. Convergence is more than the simple combination of different disciplines or technologies. It leads to synergies, adding more value through convergence.[4]
While converging technologies lead to fast and far-reaching improvements, they also create new security challenges and risks. We often try to address new risks with methods that were successful in the past; however, they may not be appropriate for the systemic risks posed by the increasing interconnectivity and complexity associated with converging technologies.[4] Additionally, with highly interconnected systems, the risk from dependencies and interdependencies must be considered. Therefore, we must take a more systemic approach to assessing and mitigating risks resulting from converging technologies.
Emerging and converging technologies have significantly increased the number of vulnerabilities to national security to levels that are untenable for the government and private sector to address in their entirety. They simply do not have the resources required to implement mitigation strategies to address risks with a low probability of occurrence and/or low consequence. Current conversations do not prioritize potential courses of action based on defensible integrated risk assessments that consider both probability and consequence in the context of converging technologies.
Cyberbiosecurity
The exploration of life sciences has become increasingly dependent upon internet-connected machinery and devices. Internet-dependent infrastructure is critical to computation and discovery of new avenues of research. The subsequent dependence upon technology and internet-connected devices begs the need to secure this infrastructure. For example, attackers could exploit unsecured networks and remotely manipulate biological material, creating new threats with devastating potential.[3] Cyberbiosecurity aims to understand and reduce the risks associated with conducting research using advanced technologies in the bioscience field. Science exploration depends increasingly upon cloud services, cyber-physical devices, internet-connected machines, remote databases, and many other cyber-vulnerable technologies. This convergence of science and cybersecurity opens the field to a new threat landscape.
Below are two examples of vulnerabilities that may not be individually identifiable in either a biosecurity or a cybersecurity context but are only apparent when both disciplines are considered.
Bringing together advances in synthetic biology and genetic engineering with machine learning, advanced modeling, metabolic engineering, and access to publicly available databases containing complete genome sequences of pathogens, including virulence factors, will enable the design of novel high consequence biological agents completely in silico. Minimal laboratory infrastructure and equipment would be required. Moreover, the vast array of publicly available open-source tools enable execution of these processes by less experienced personnel.
Advances in laboratory automation have enabled tacit knowledge (e.g., hands-on know-how), traditionally requiring years of professional laboratory training, to be codified into executable code controlling automated laboratory equipment. The ability of automated laboratory equipment to reproducibly perform tasks—once limited to well-trained laboratorians—has been monetized in the form of commercial biological production facilities (e.g., biofoundries). These biofoundries may unwittingly produce components of high-consequence biological agents solely from digital information provided by the customer. To request synthesis services, the customer simply goes to the website of the biofoundry and uploads the required biological data (e.g., DNA sequences, amino acid sequences, etc.). To obscure the identity and/or functional properties of the final product, several biofoundries can be used, each synthesizing seemingly innocuous products representing only a portion of the final product.
Furthermore, contributions to the exploration of science are built upon the open and sharing nature of samples and knowledge. This inherent openness and trust that exist in the scientific community is ripe for exploitation.[2] In order to thwart attackers and keep data secure, it is paramount that the CIA triad of confidentiality, integrity, and availability of scientific data is upheld in this digital era. Compromising any of the pillars within the CIA triad could lead to unwanted consequences. For example, attackers could:
- exploit vulnerable infrastructure and steal proprietary sequences from a biotechnology firm, ruining the confidentiality of the stolen intellectual property;
- manipulate DNA sequences for malicious intent, thereby destroying the integrity of a given sample or changing a sample to be something other then what is intended; or
- degrade systems, compromising the availability of cyber-physical devices that are used to perform needed functions.
Ensuring the confidentiality, integrity, and availability of both the physical material and the associated digital information is essential to ensuring the safety and security of scientific advances in bioscience.
Understanding key terms
Defining the key elements of the emerging field of cyberbiosecurity is important to ensuring a common understanding of the relevant technical issues that arise from this new hybrid discipline. It is equally important to define key terms related to risk, particularly for audiences that may not already be familiar with the core concepts relevant to biosecurity, cyber-physical security, and cybersecurity assessments, policies, and practices. An important foundational document in this regard is the DHS Risk Lexicon, published in 2010 by the U.S. Department of Homeland Security to level-set terminology across the homeland security enterprise.[5]
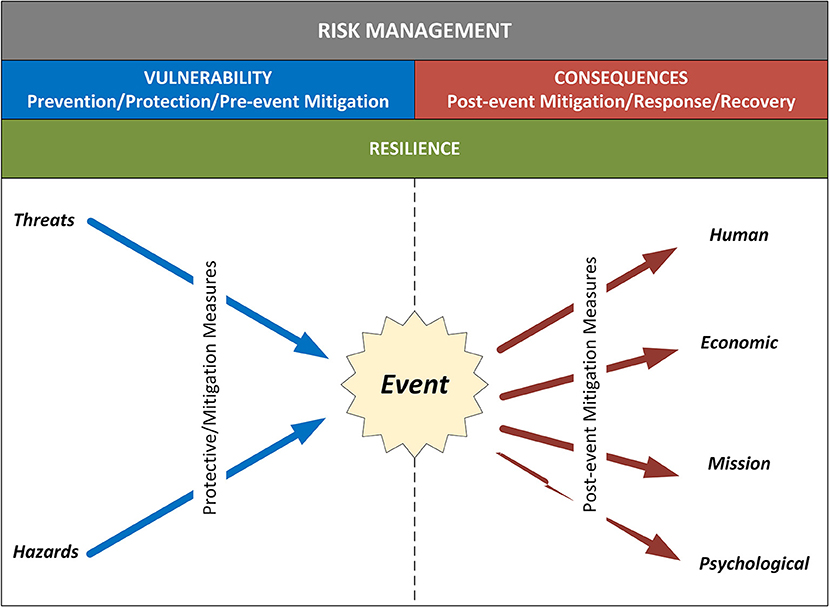
As framed in the DHS Risk Lexicon, risk is the potential for an unwanted outcome resulting from an incident, event, or occurrence, as determined by its likelihood and the associated consequences. Evaluating the probability of adversarial attacks is challenging due in part to the lack of historical data in which to ground quantitative estimates, an inability to project that future deliberate threats will resemble those of the past, and the inherent challenges in evaluating the intent and capability of entities seeking to exploit weaknesses. Thus, risk in the Homeland Security space has been framed as a function of three elements: the threats to which an asset or system is susceptible, the vulnerabilities of the asset or system to the threat, and the potential consequences arising from the degradation of the asset or system. Each of these elements is defined below[5]:
- Threat
- natural or human-caused occurrence, individual, entity, or action that has or indicates the potential to harm life, information, operations, the environment, and/or property
- Vulnerability
- physical feature or operational attribute that renders an entity open to exploitation or susceptible to a given hazard
- Consequence
- the effect of an event, incident, or occurrence; consequence is commonly deconstructed and measured in four categories: human, economic, mission, and psychological
When talking about risk, it is also important to define what a hazard is due to its direct correlation and impact on vulnerabilities, threats, and consequences of an asset. A hazard is a natural or man-made source or cause of harm or difficulty. Threats are typically directed at an entity, asset, system, network, or geographic area, while a hazard is a natural or accidental phenomenon that is not driven consciously by an adversary.
Although not typically identified as one of the three core factors driving risk, resilience is an additional consideration that impacts assessments of risk and ensuing strategies for managing it. As a result, it is relevant to understanding ways to evaluate cyberbiosecurity. Resilience is the ability to resist, absorb, recover from, or successfully adapt to adversity or a change in conditions.[5] Resilience features play a role in both the vulnerability and consequence variables in risk. Resilience measures can reduce vulnerability to various threats and hazards through protective measures that improve an organization's ability to resist an event or absorb its effects with minimal impact. Similarly, on the consequence side, resilience measures can enhance an entity's ability to quickly adapt and respond to an incident, as well as to recover and return to normal operations more quickly.[5][6]
Taking into consideration all of these inputs, organizations can institute defensible, repeatable, and actionable processes to analyze risk and ultimately, to make decisions on how to manage it. Risk management is the process of identifying, analyzing, and communicating risk and then accepting, avoiding, transferring, or controlling it to an acceptable level and at an acceptable cost.[5] Risk management involves knowing the threats and hazards that could potentially impact a given organization, the vulnerabilities that render it susceptible to particular hazards, and the various consequences that might result. Figure 1 illustrates how these various components combine to drive risk-based decision-making.[7]
|
Cyberbiosecurity is a new field that brings together different disciplines in new ways, triggering a pressing need for new thinking in terms of relevant threats, vulnerabilities, and consequences. Existing approaches used in biosecurity, cyber-physical security, and cybersecurity communities provide important foundational concepts and organizing principles, but they do not adequately capture emergent features related to biological and biomedical systems. Biosecurity, cyber-physical security, and cybersecurity are defined below.
- Biosecurity
- describes the protection, control, and accountability of biological materials in order to prevent their unauthorized access, loss, theft, misuse, diversion, or intentional release
- Cyber-physical security
- addresses the potentially high-consequence dependency between physical systems and the special-purpose computers that control and monitor them
- Cybersecurity
- addresses the risks of computer and network systems used for managing processes and sharing and protecting information
References
- ↑ Wintle, B.C.; Boehm, C.R.; Rhodes, C. et al. (2017). "A transatlantic perspective on 20 emerging issues in biological engineering". eLife 6: e30247. doi:10.7554/eLife.30247. PMC PMC5685469. PMID 29132504. https://www.ncbi.nlm.nih.gov/pmc/articles/PMC5685469.
- ↑ 2.0 2.1 Peccoud, J.; Gallegos, J.E.; Murch, R. et al. (2018). "Cyberbiosecurity: From Naive Trust to Risk Awareness". Trends in Biotechnology 36 (1): 4–7. doi:10.1016/j.tibtech.2017.10.012. PMID 29224719.
- ↑ 3.0 3.1 Murch, R.S.; Wo, W.K.; Buchholz, W.G. et al. (2018). "Cyberbiosecurity: An Emerging New Discipline to Help Safeguard the Bioeconomy". Frontiers in Bioengineering and Biotechnology 6: 39. doi:10.3389/fbioe.2018.00039. PMC PMC5895716. PMID 29675411. https://www.ncbi.nlm.nih.gov/pmc/articles/PMC5895716.
- ↑ 4.0 4.1 Dengg, A., ed. (2018) (PDF). Tomorrow's Technology: A Double-Edged Sword. Federal Ministry of Defence, Republic of Austria. ISBN 9783903121317. http://www.bundesheer.at/pdf_pool/publikationen/buch_dengg_tomorrows_technology_web.pdf.
- ↑ 5.0 5.1 5.2 5.3 5.4 Risk Steering Committee (September 2010). "DHS Risk Lexicon, 2010 Edition" (PDF). Department of Homeland Security. https://www.dhs.gov/sites/default/files/publications/dhs-risk-lexicon-2010_0.pdf.
- ↑ Petit, F.D.P.; Bassett, G.W.; Black, R. et al. (15 July 2013). "Resilience Measurement Index: An Indicator of Critical Infrastructure Resilience". Argonne National Laboratory. doi:10.2172/1087819. https://www.osti.gov/biblio/1087819-resilience-measurement-index-indicator-critical-infrastructure-resilience.
- ↑ Petit, F.D.P.; Bassett, G.W.; Buehring, W.A. et al. (21 November 2013). "Protective Measures Index and Vulnerability Index: Indicators of Critical Infrastructure Protection and Vulnerability". Argonne National Laboratory. doi:10.2172/1108161. https://www.osti.gov/biblio/1108161.
Notes
This presentation is faithful to the original, with only a few minor changes to presentation, grammar, and punctuation. In some cases important information was missing from the references, and that information was added.